Somewhere in your organization, a vendor is pitching "zero trust" as a product. It comes in a box -- or more likely, a SaaS dashboard. Buy the license, deploy the agent, flip the switch, and congratulations: you're now zero trust. Except you're not. You've purchased a tool and slapped a label on it. The network perimeter you thought you eliminated is still there. You've just moved it and added a login screen.
Zero trust is not a product. It's not a platform. It's not something you can buy from a vendor at RSA. It's an architectural principle -- a way of designing systems that assumes no actor, no device, no network segment is inherently trustworthy. Every request is verified. Every session is validated. Every permission is scoped to the minimum required. That's it. That's the whole idea. And yet, the gap between that principle and what most organizations actually implement is enormous.
The Perimeter Is Dead. You Just Haven't Buried It.
Traditional network security operated on a castle-and-moat model. Everything inside the firewall was trusted. Everything outside was not. Get past the drawbridge, and you had the run of the place. VPNs extended this model -- they punched a tunnel through the moat so remote workers could get inside the castle walls.
This model was already fragile before the cloud. It assumed that internal traffic was benign, that lateral movement wasn't a concern, and that the perimeter was clearly defined. None of those assumptions held up. Breaches happened. Attackers got inside the network and moved freely because nothing inside challenged their presence. The 2013 Target breach is the textbook example -- attackers compromised an HVAC vendor, used that foothold to move laterally through the network, and exfiltrated 40 million credit card numbers. Everything inside the perimeter trusted everything else.
Cloud and hybrid architectures shattered whatever remained of the perimeter concept. Your applications run in three cloud providers, your employees work from coffee shops, your data flows through SaaS platforms you barely control. Where exactly is the perimeter? There isn't one. And if there's no perimeter, a security model that depends on one is worse than useless -- it's a false sense of safety.
What Zero Trust Actually Means
The core tenets are straightforward. First: assume breach. Design every system as if an attacker is already inside your network, because statistically, they probably are -- or will be. The average dwell time for an undetected breach is still measured in months. Your architecture should limit the blast radius of a compromise, not assume compromises don't happen.
Second: verify explicitly. Every request -- whether it comes from a user, a service, or a device -- must be authenticated and authorized based on all available data points. Not just "do they have a valid session token?" but "is this device compliant? Is this request consistent with their normal behavior? Is the network context expected?" Verification isn't a gate you pass through once. It's continuous.
Third: least privilege. Every identity gets the minimum permissions needed for the task at hand, and those permissions are scoped as narrowly as possible. Not "admin access to production" but "read access to this specific database table for the next 30 minutes." This applies to humans, services, CI/CD pipelines, everything. If a compromised service account can read every secret in your vault, your least privilege implementation is theater.
The BeyondCorp Model
Google's BeyondCorp initiative -- published starting in 2014 -- is the most influential real-world implementation of zero trust principles. The core insight was radical for its time: access to internal applications should not depend on what network you're connected to. An employee on the corporate LAN should go through the same authentication and authorization as an employee at a coffee shop.
BeyondCorp replaced VPN-based access with an access proxy that evaluates every request against device trust, user identity, and contextual signals. The network became a transport layer, not a trust boundary. An employee's laptop needed to meet specific security posture requirements -- encrypted disk, up-to-date OS, managed device certificate -- regardless of where it connected from.
This is the part most organizations miss when they claim to implement zero trust. They add an identity provider and call it done. But BeyondCorp wasn't just about authentication. It was about continuous evaluation of trust signals across every dimension: identity, device health, request context, behavioral patterns. If any signal changed -- if a device fell out of compliance, if a login came from an unusual location -- access was re-evaluated in real time.
Microsegmentation: Actually Limiting Blast Radius
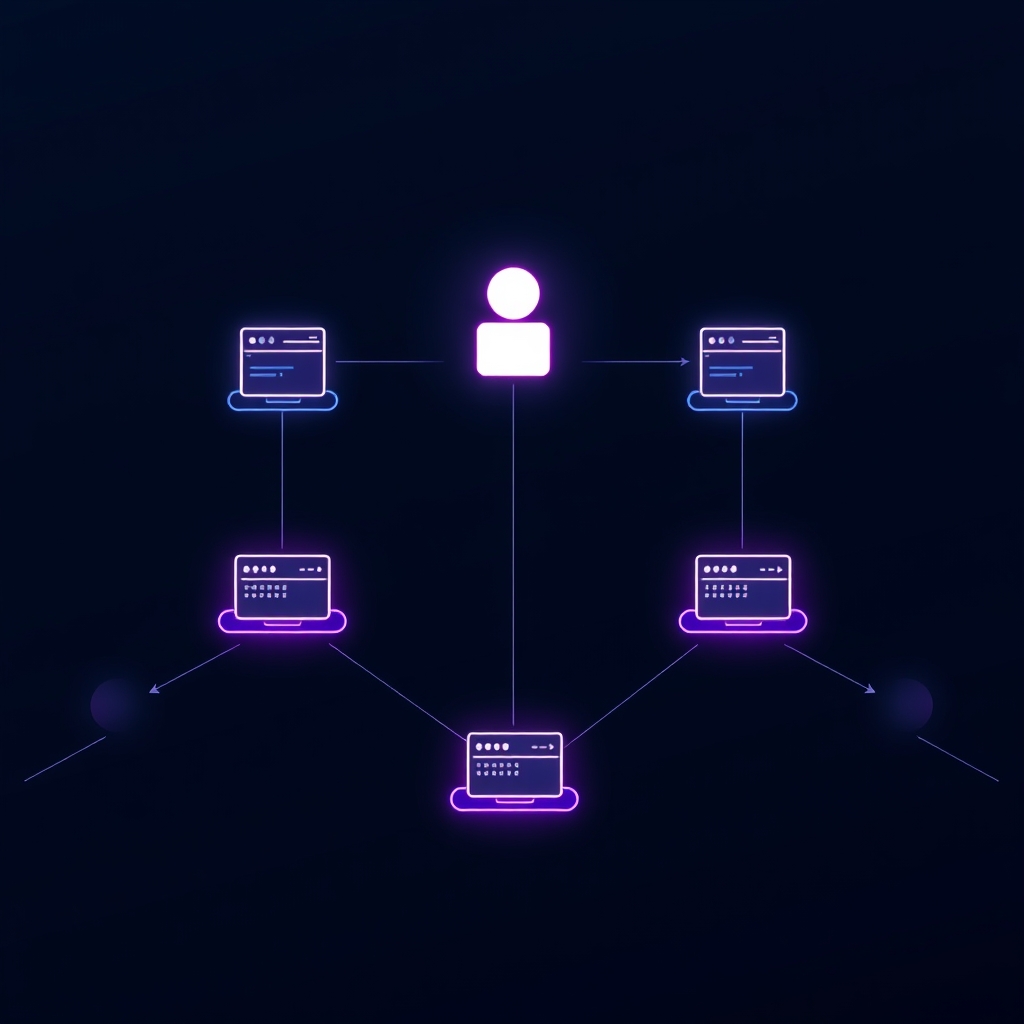
Zero trust without microsegmentation is incomplete. You can verify identity perfectly, but if a compromised workload can talk to every other workload in your network, you've limited nothing. Microsegmentation enforces that services can only communicate with the specific other services they need to -- and nothing else.
In practice, this means defining network policies at the workload level, not the subnet level. Service A can talk to Service B on port 443. Service A cannot talk to Service C at all. This is a massive shift from traditional flat networks where anything in the same VLAN can reach anything else.
Kubernetes network policies are one implementation. Cloud security groups are another. Service mesh sidecars that enforce mutual TLS and authorization policies are a third. The mechanism matters less than the principle: every communication path must be explicitly allowed. Default deny. If you haven't defined a policy permitting the traffic, the traffic doesn't flow.
The operational cost of microsegmentation is real. You need to understand your service dependencies thoroughly before you can define policies. Turn on default-deny without a complete dependency map and you'll cause an outage. But the security payoff is substantial. When an attacker compromises one service, they can only reach the handful of services that the compromised workload was explicitly permitted to contact. Lateral movement goes from trivial to extremely difficult.
Mutual TLS: Trust the Connection, Not the Network
Standard TLS gives you server authentication -- the client verifies it's talking to the right server. Mutual TLS (mTLS) adds client authentication -- the server also verifies the client's identity via certificate. Both sides present certificates. Both sides verify. Nobody trusts the network to guarantee identity.
This is foundational to zero trust service-to-service communication. When Service A calls Service B, mTLS ensures that Service B can cryptographically verify it's actually talking to Service A -- not an attacker who happens to be on the same network. The network path is irrelevant. The certificate is the identity.
Implementing mTLS at scale requires serious infrastructure investment. You need a certificate authority, automated certificate issuance and rotation, a way to distribute trust bundles, and monitoring for certificate expiration. Service meshes like Istio and Linkerd abstract much of this complexity, but they introduce their own operational overhead. The point isn't that mTLS is easy. The point is that without it, your service-to-service communication is trusting the network -- which is the exact thing zero trust says you shouldn't do.
Identity Is the New Perimeter
If you take one thing from zero trust, it's this: identity replaces the network as the primary security boundary. Every access decision is based on who or what is making the request, not where the request comes from.
This requires a robust identity foundation. For humans: strong authentication (hardware keys, not just passwords), centralized identity providers, conditional access policies that evaluate device compliance and session risk. For services: workload identity (SPIFFE/SPIRE, cloud IAM roles, Kubernetes service accounts) with short-lived credentials that are automatically rotated. For devices: device trust evaluation that checks patch level, encryption status, and management enrollment.
The mistake I see most often is treating identity as a boolean. Authenticated? Yes. Authorized? Yes. Done. But identity in a zero trust model is multidimensional. It's the combination of who you are, what device you're using, where you're connecting from, what you're trying to access, and whether the pattern is consistent with your normal behavior. A valid credential used from an unfamiliar device in an unusual geography at 3 AM should not be treated the same as a valid credential used from a managed device during business hours.
Zero Trust Marketing vs. Zero Trust Reality
The security industry has done what it always does with a good idea: commercialized it into incoherence. "Zero trust" now appears on every vendor's marketing page. ZTNA (Zero Trust Network Access) products have replaced VPNs -- which is fine as far as it goes, but it's one piece of a much larger architecture.
Here's a quick diagnostic for whether your "zero trust implementation" is marketing or substance:
- Marketing: You bought a ZTNA product and retired your VPN. Reality: You still have flat internal networks with no microsegmentation, and internal services communicate without mutual authentication.
- Marketing: You require MFA for user login. Reality: Service accounts use long-lived static credentials with broad permissions, and nobody reviews whether those permissions are still needed.
- Marketing: You have a "zero trust" checkbox on a compliance report. Reality: You haven't mapped your service dependencies, you can't describe your trust boundaries, and a compromised workload could reach any database in production.
Real zero trust is uncomfortable. It forces you to answer hard questions about your architecture. What are the trust boundaries? Who can access what, and why? What happens when a credential is compromised? How far can an attacker move before something stops them? If you can't answer those questions concretely, you don't have zero trust. You have a vendor contract.
Practical Implementation Steps
Zero trust is not a project with a completion date. It's an ongoing architectural discipline. But you have to start somewhere. Here's a pragmatic path:
- Map your identity landscape. Inventory every human identity, service account, API key, and machine credential in your environment. You can't apply least privilege to identities you don't know about. This step alone will be sobering -- most organizations have 3-5x more service accounts than they expect.
- Enforce strong authentication everywhere. Hardware security keys for humans. Short-lived, automatically rotated credentials for services. Eliminate long-lived API keys and shared secrets. If a credential doesn't expire, it's a liability.
- Map your network dependencies. Before you can microsegment, you need to understand what talks to what. Run your services in audit mode first -- log all connections without blocking. Use the data to build a dependency graph. Then start defining policies.
- Implement default-deny network policies. Start with your most sensitive workloads. Database access should be explicitly granted to specific services, not available to anything on the same network. Expand outward from there.
- Add continuous verification. Move beyond one-time authentication. Evaluate device compliance, session risk, and behavioral signals on an ongoing basis. Revoke or step up authentication when signals change.
- Encrypt everything in transit. mTLS for service-to-service. TLS for everything else. If traffic traverses a network -- any network -- it should be encrypted and authenticated. The performance overhead of TLS in 2026 is negligible. The excuse for plaintext internal traffic no longer exists.
Each of these steps is individually valuable. You don't need to complete all six before you see security improvements. But together, they represent a fundamental shift from perimeter-based security to identity-based, continuously-verified, least-privilege architecture. That's zero trust. Not a product. Not a checkbox. A way of building systems that assumes the worst and verifies everything.
The goal isn't to build an impenetrable fortress. It's to build a system where every breach is contained, every access is justified, and every assumption is replaced with verification.
Zero trust is hard. It requires investment, discipline, and a willingness to challenge the convenient fictions that perimeter security was built on. But the alternative -- trusting your network, trusting your perimeter, trusting that the attacker isn't already inside -- is a bet you will eventually lose. The question isn't whether to adopt zero trust principles. It's whether you do it before or after the breach that proves you needed them.